How to hack elections on Georgia’s electronic voting machines
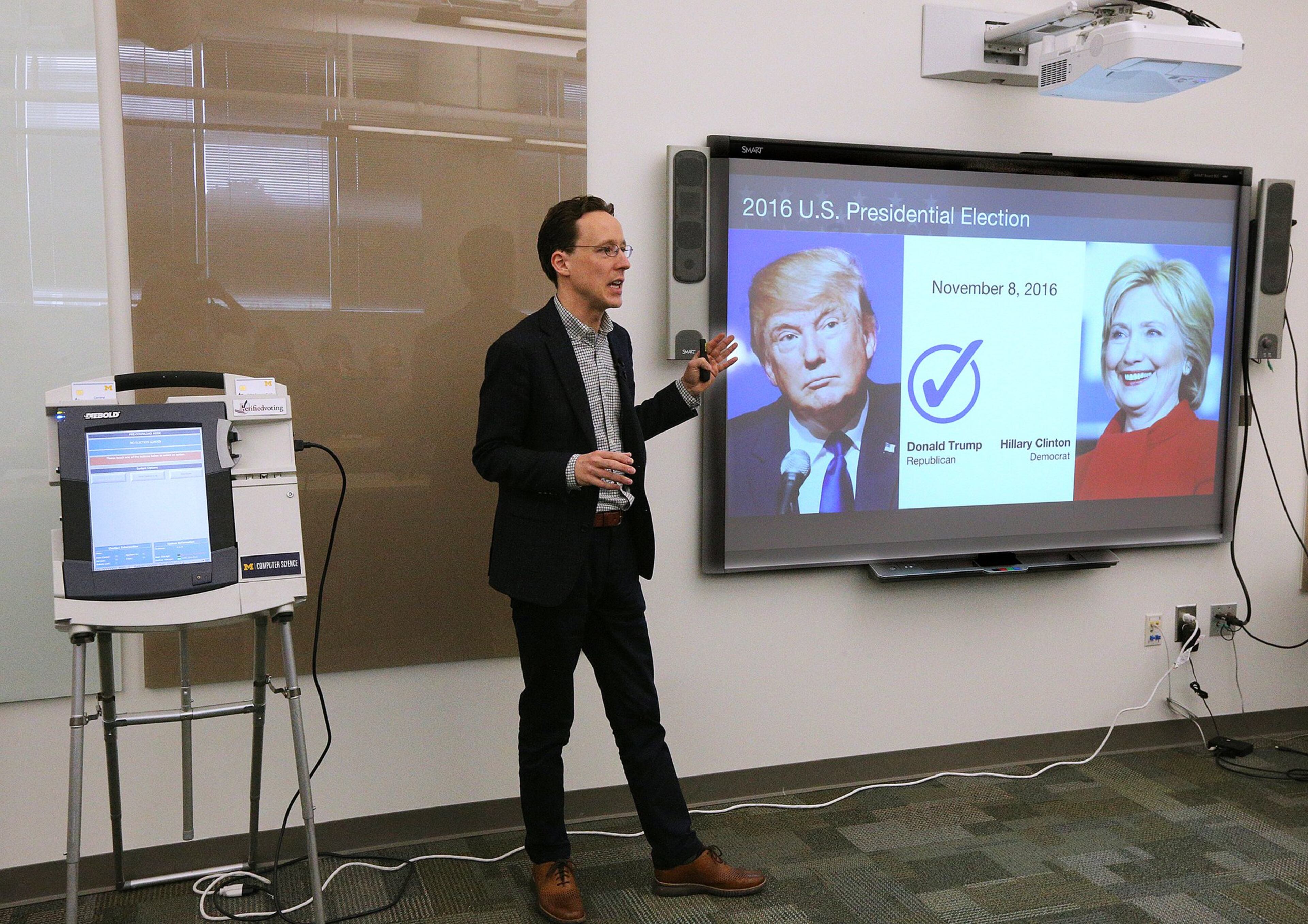
A rapt audience watched as professor Alex Halderman, an expert on electronic voting machines, changed votes in a hypothetical election before their eyes.
At a Georgia Tech demonstration this week, Halderman showed how to rig an election by infecting voting machines with malware that guaranteed a chosen candidate would always win.
Four people from the audience voted on the same kind of touch-screen machines used in real Georgia elections, casting ballots for either President George Washington or Benedict Arnold, the Revolutionary War general who defected to the British. Despite a 2-2 split in this election test run, the voting machine’s results showed Arnold won 3-1.
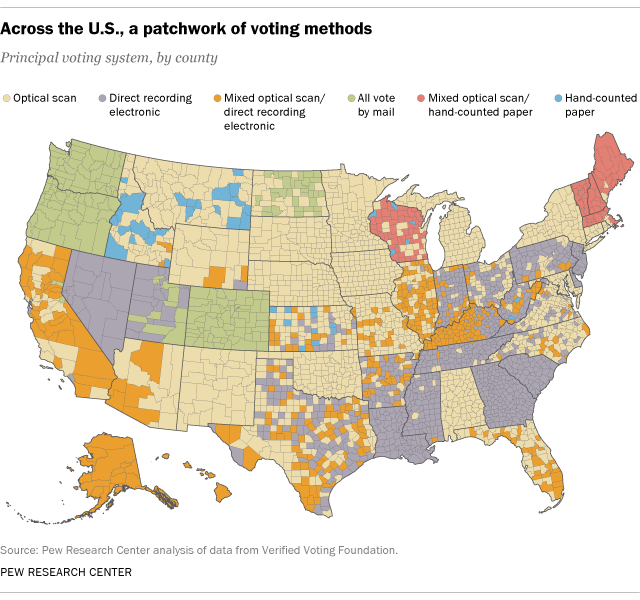
Halderman's hack is a warning to Georgia, one of five states that relies entirely on electronic voting machines without an independent paper backup. Nationwide, 31 states use direct-recording electronic devices on Election Day to some extent.
“Voting is not as safe as it needs to be,” Halderman, a computer science professor at the University of Michigan, said Monday. “The safest technology is to have voters vote on a piece of paper.”
The upcoming May 22 primary elections will continue to use these touch-screen machines, but state legislators are considering switching to a voting system with a paper record for accuracy, possibly in time for the 2020 presidential election.
There’s no evidence that Georgia’s election systems have been tampered with. But Halderman said it’s only a matter of time before foreign countries such as China, Iran, North Korea or Russia try to undermine elections by penetrating voting infrastructure in the United States.
Russian hackers already attempted to interfere with the 2016 presidential campaign by targeting election systems in 21 states, the U.S. Department of Homeland Security said in August 2016. Georgia wasn’t one of those states. In addition, 13 Russians were charged this year on allegations they tried to influence the election through social media propaganda.

For Halderman’s demonstration, he wrote a program to alter the results of elections recorded by AccuVote touch-screen voting machines. He installed that program on a rectangular memory card that fits into the side of the machine, allowing the card to infect the machine.
If a hacker penetrated the state’s computer servers, a similar malicious program could be copied to memory cards used for each of the 27,000 voting machines across the state, Halderman said. No one would ever know the results had been changed if the hacker wrote the program to erase itself after the election.
Candice Broce, a spokeswoman for Georgia Secretary of State Brian Kemp, said Halderman’s concerns are addressed by state law, regulations and security procedures. State election systems use data encryption and aren’t connected to the internet.
“We are prepared,” Broce said. “There are logical and physical safeguards in place for each aspect of the voting system. Halderman would be unable to replicate this outcome in Georgia’s current security environment.”
She didn’t provide details about Georgia’s security practices, but Halderman said hackers could find a way.
He said hackers could infect election computers by first gaining access to a state employee’s computer, possibly by tricking him or her into clicking on a dangerous link in an email. Once the malware is on one machine, it could reach central election systems through internal networks, USB devices or memory cards.
Election computers could also be subverted in person, by someone like a janitor or a temporary worker, Halderman said. Individual voting machines could be tampered with if someone unlocked the latch that protects the memory card port.
State Rep. Scot Turner said Georgia's elected officials should get rid of the state's electronic voting machines as responsibly and as quickly as possible.
“When you see a machine flip votes, you have to admit things are vulnerable,” Turner, a Republican from Holly Springs, said after watching Halderman’s demonstration. “It might take a wide-scale effort to do what he did on a statewide basis, but it can be done. We owe it to the voters to make sure it’s not.”
More than 70 percent of U.S. voters use paper ballots, usually by filling in bubbles next to a candidate's name and then inserting ballots into a tabulation machine.
Some jurisdictions use touch-screen machines to print ballots before they're scanned for tabulation.
A bill that would have replaced Georgia's electronic voting machines with a paper-backed system failed to pass this year amid disagreements over which election technology to use. A primarily paper-based system would cost $35 million or more, while a touch screen-and-paper system could cost well over $100 million.
Any technology can be hacked, but hand-marked paper ballots provide a way to recount and audit elections to ensure they delivered fair results, said Halderman, a member of the board of directors for Verified Voting, a Philadelphia-based organization whose mission is to safeguard elections.
“We have to move to a different way of doing things so in case anything happens, we can recover. That’s what a voter-marked paper ballot does,” said Marian Schneider, the president of Verified Voting.
Georgia's election system had a security lapse in the recent past, when a researcher discovered that Kennesaw State University's Center for Election Systems had exposed the personal information of 6.7 million Georgia voters online.
The breach, which was closed in March 2017, resulted in the state ending its nearly $800,000 annual contract with KSU and bringing elections administration work in-house to the Secretary of State’s Office.
Technology experts had previously exposed security vulnerabilities in electronic voting machines in July during the DefCon computer hacking conference in Las Vegas.
Unlike Halderman’s work, the groups at DefCon weren’t trying to change votes. They focused on finding potential weaknesses in voting systems.
Halderman took the hacks a step further. He wrote the malware program and installed it on the memory card and touch-screen voting machine.
“Every vote in the state is potentially at risk,” Halderman said. “Usually, each voting machine will get its own individual memory card, but it all comes from the same source. If that computer is infected with malicious software, it could spread across the state.”